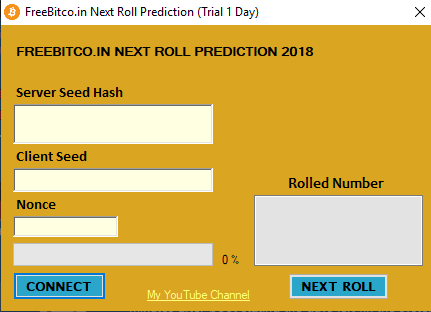
Analysis of FreeBitco.in Next Roll Prediction
Malware obtained from any.run. It’s a bitcoin scam executable.
| Property | Value |
|---|---|
| MD5 | afb30fed336e9b1e5e8ea5d941691b2a |
| SHA1 | afeb330ea75da11608bc4f32d3490ed38cfd4c11 |
| SHA256 | 16b4664969ce27b9914dc9d41b5baa16a341e00f442527efffd478a73a014fa1 |
2 EXEs dropped
Running procmon when running the malware shows that 2 possibly interesting executables are created: C:\Users\IEUser\AppData\Roaming\Microsoft\gons.exe and C:\Users\IEUser\AppData\Roaming\Microsoft\temp5789e.exe. Both of these dropped executables are .NET assemblies, so they should be trivial to reverse.
gons.exe
Opening gons in dnSpy shows that this executable is responsible for the GUI, and I didn’t notice any malicious behaviour initially.
It’s simply a form with the typical MyXXX structure, nothing interesting.
temp5789.exe
I noticed calls to System.RuntimeCompilerServices.RuntimeHelpers, so let’s see if there is dynamically loaded code.
Using Process Hacker, we can simply check the process and see the .NET assemblies. Interestingly, there is one assembly within the app’s domain called Nuclear Explosion, which has a path of Nuclear Explosion, so it must have been dynamically loaded in as suspected.
To dump Nuclear Explosion, I’ll use the great tool by wwh1004 called Extreme Dumper. It’s a very nice and simple tool, just select dump selected process for the running malware sample.
Nuclear Explosion.exe
Here I believe is the real meat of the malware, with plenty of nice obfuscation to add. Running it through de4dot removes the filler nonsense classes and some of the obfuscation.
In the only class, Nuclear_Explosion.Atomic, there seems to be several references to sockets, suggesting that something is downloaded, along with more references to dynamic code loading. It’s likely that this downloads other .NET malicious software, but more analysis is needed.
It also fingerprints the machine through information such as the processor, system drive information and a driver. Interestingly there’s also some SQL querying from the tables AntiVirusProduct and FirewallProduct.
The method data takes the beginning of a series of bytes and compares them to several strings, such as PNC, P, IE, LP and UNV. Here’s a basic analysis of what each command does:
| Command | Action |
|---|---|
| PNC | response: PNC |
| P | reponse: Title of current window |
| IE | response: registry keys |
| LP | action: Sets registry keys |
| UNV | action: Dynamically load received code |
The obvious
If I look at Nuclear_Explosion.Atomic.Key, I see that it’s statically set to "Revenge-RAT". Clearly I was going a bit ahead of myself earlier.
I’ve identified the control server as ytka.duckdns.org:5552. When I ping this, I receive a response from sinkhole.hyas.com.
The malware has been sinkholed by HYAS, thank you for preventing this RAT from affecting users.